PSA: PGP/GPG and S/MIME vulnerabilities found
Earlier today, a group of European researchers from Münster University, Ruhr-University, and KU Leuven University released a warning on Twitter:
We'll publish critical vulnerabilities in PGP/GPG and S/MIME email encryption on 2018-05-15 07:00 UTC. They might reveal the plaintext of encrypted emails, including encrypted emails sent in the past. #efail 1/4
— Sebastian Schinzel (@seecurity) 14 May 2018
The EFF advises completely disabling PGP/GPG and S/MIME from your email client as a temporary measure. There are guides for Enigmail on Thunderbird, AppleMail with GPGTools and Outlook with Gpg4Win.
Our advice, which mirrors that of the researchers, is to immediately disable and/or uninstall tools that automatically decrypt PGP-encrypted email.
The details of the exploit have not yet been released, but the early description looks like RCE (Remote Code Execution).
This vulnerability might be used to decrypt the contents of encrypted emails sent in the past. Having used PGP since 1993, this sounds baaad. #efail
— Mikko Hypponen (@mikko) 14 May 2018
EFF's recommendation is to use an alternative end-to-end secure channel such as Signal.
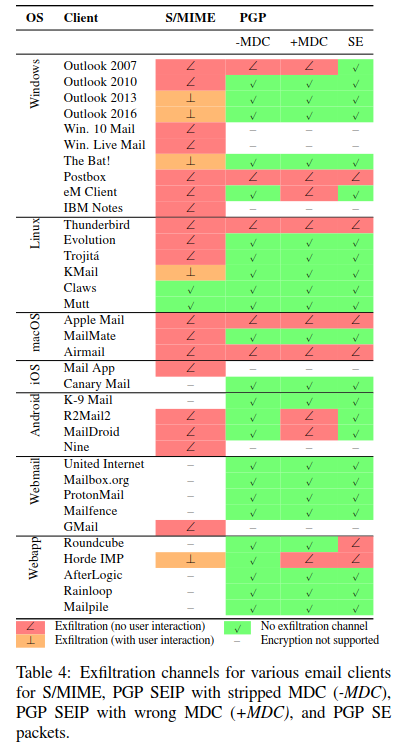
UPDATE: The vulnerability is not in the protocol itself, but rather in the implementation in various email clients.
Here is a chart listing the vulnerable email clients: