KRACK in Wi-Fi : severe flaw discovered in WPA2 protocol
A security problem with Wi-Fi networks has been discovered. Wifi is everywhere : chances are you use it at home and at work. And this time, it's not even about the dangers of open, unsecured networks : WPA2, the standard encryption protocol for all secured networked has been breached.
The problem is that an attacker physically near you can now eavesdrop your traffic if it's not further encrypted (by a VPN for example).
However, not all platform are impacted in the same way : Android and Linux are now most at risk. Fortunately there's something you can do (or will be able to doo soon) : installing security updates.
A group of security researchers released details about a vulnerability in WPA2, the security protocol used in most password-protected Wi-Fi networks. As with all security flaws, it allows a malicious actor to perform attacks (called KRACKs, for key reinstallation attacks) to read the information circulating between your computer and the router, that is to say the wireless access point you're connected to access the internet.
Usually, information is encrypted with WPA2 AES or TKIP, but some flaws have been discovered in the system itself, that allow attackers to "steal sensitive information such as credit card numbers, passwords, chat messages, emails, photos, and so on" according to the researchers' website.
if your device supports Wi-Fi, it is most likely affected.
You shouldn't think that this only impacts old devices : Windows, Android, Linux, Apple, OpenBSD, Mediatek (maker of phone platforms), Linksys, Netgear... the list of affected product is virutally endless.
In some cases, it is even possible for the attacker to modify unencrypted websites (website without HTTPS in front of their address) to inject malware and in particular ransomware.
The technical side of the vulnerability
Technically, the attack is against what is called the handshake, that is is to say the process where you device talks to the router to authenticate.
An attacker can copy your WPA2-protected network by impersonating the MAC address of your router, and changing its WiFi channel. This new, fake network acts as a "man in the middle" (MiTM attack) so when a device attempts to connect to your real router's wifi network, it can be forced to bypass it and connect to the rogue, fake one.
In a KRACK (key reinstallation attack), the attacker trick you into reinstalling an already-in-use key. It can be done by modifying and replaying (resending) cryptographic handshake messages.
When a key is reused, the the incremental transmit packet number and replay counter (receive packet number) are basically reset.
If your router is using either the WPA-TKIP or GCMP encryption protocols, instead of AES-CCMP, the practical impact is even worse. With these encryption protocols, nonce reuse enables an adversary to "not only decrypt, but also to forge and inject packets", thus making the injection of ransomware a possibility.
What you can do
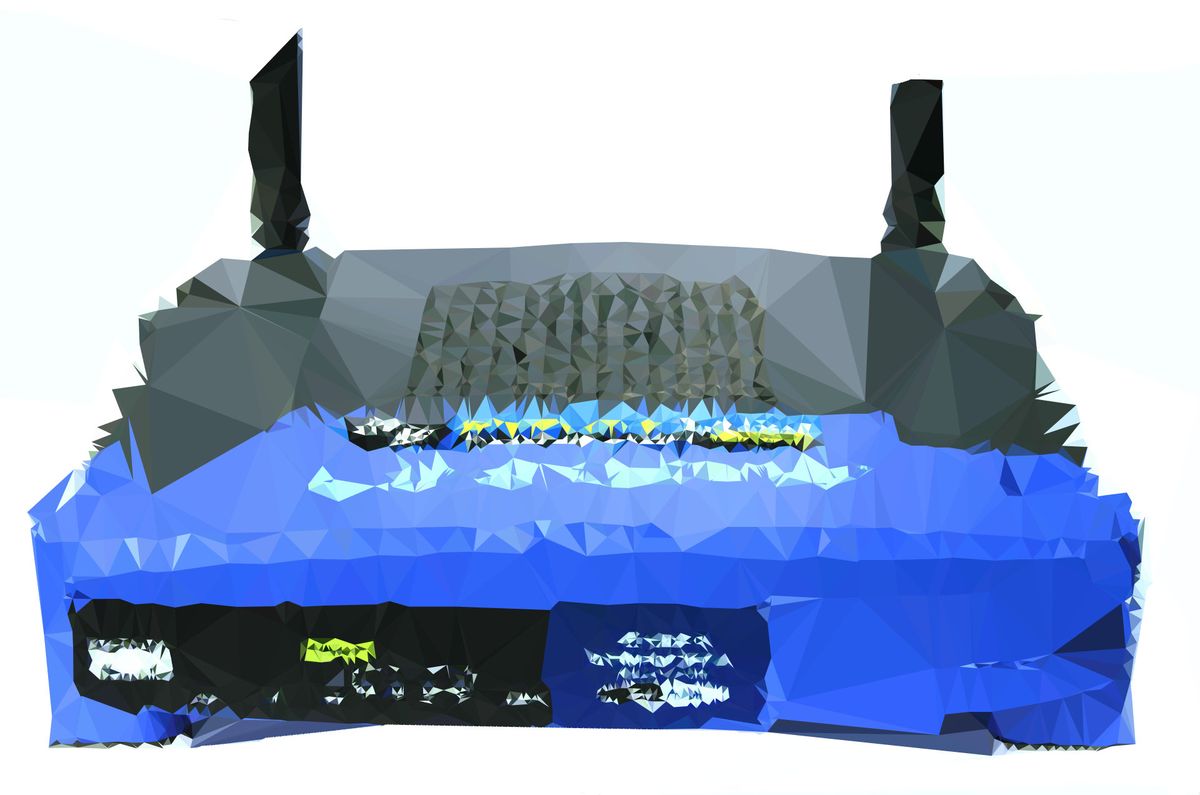
The only way to protect yourself is to apply security updates to your devices, and (now comes the difficult part) to your router.
The Linux patch is already available, but OEMs (device makers) need to manually modify them with their cutomizations before releasing new versions of their products's firmware.
The problem is that usually, you cannot update your ISP's modem/router. More often than not, the router included with your subscription cannot be updated by the end-user (you).
However, if you have you own router, don't forget to check for updates regularly in its web interface. You can usually access it by typing something like 192.168.0.1 in your browser address bar. Please refer to the website of your device maker for further information, as this varies from one brand to another.
The firmware update will force your router to require a dedicated certificate for each handshake, instead of relying on one that has already been generated.